The Mobile Bunker: Encryption on GrapheneOS (Termux Edition)

Secure encryption on the go with GrapheneOS and Termux — a workflow for true sovereignty.
von Alien Investor
#GrapheneOS #Termux #Encryption #GPG #Privacy #Android #OPSEC #Sovereignty
────────────────
„No magic. Just math. That is the Alien Investor way.“
────────────────
Sovereignty does not end at the edge of your desk. You need to take your digital fortress with you.
In the first part, we built the “Digital Bunker” on the Linux desktop. We learned that true security relies on auditability, not colorful apps. But investors and strategists are mobile. What good is the most secure archive at home if you need to access sensitive documents or exfiltrate data securely while on the move?
Most mobile solutions are “black boxes.” You press a button, something happens, and you hope the developer doesn’t have a master key. This is unacceptable.
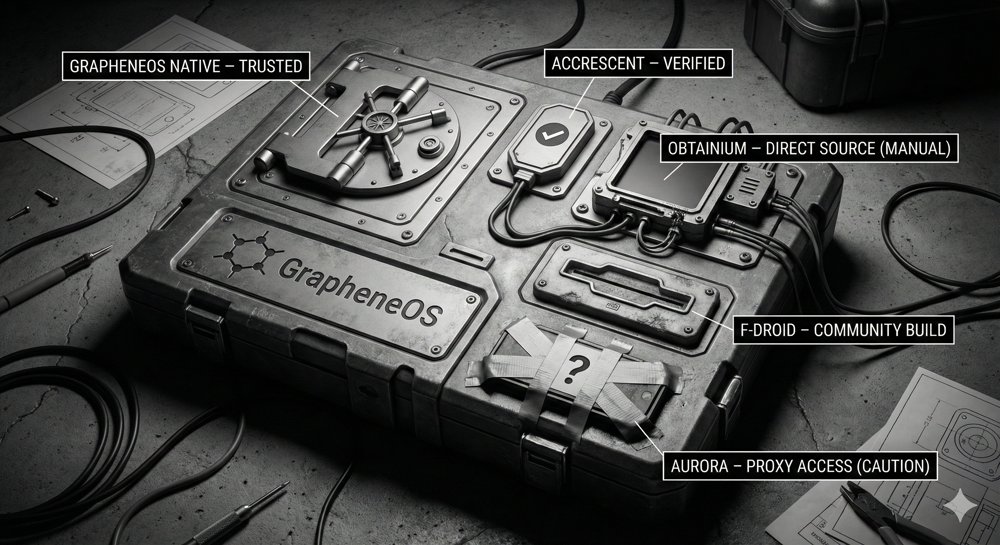
We use GrapheneOS, the only mobile operating system that takes security architecture seriously. And we use Termux, a terminal emulator that turns your smartphone into a full-fledged Linux computer.
The Goal: One workflow. Two devices. Identical math.
An archive you encrypt on your Tuxedo laptop must be openable on your GrapheneOS phone — and vice versa.
────────────────
Preparation: Setting up Termux
On GrapheneOS, it is best to install Termux via F-Droid (do not use the Play Store; the version there is outdated).
Once you have the black terminal in front of you, update the packages and install the necessary tools:
pkg update && pkg upgrade
pkg install termux-tools tar gnupg
Accessing Storage: Termux lives in isolation. For the scripts to access your downloads, we must bridge the gap to the Android file system.
termux-setup-storage
Confirm the dialog on the screen (“Allow”). Then create a folder for your tools:
mkdir -p ~/Scripts
────────────────
Part 1: The Mobile Shield (Encryption)
The encrypt-folder.sh script for Termux automatically detects if it is running on an Android system and directs the output to the Downloads folder.
Under the Hood: The Security Mechanics
Note the details in the “Helpers” section:
The Emergency Brake (die): If anything goes wrong, the script aborts immediately. It doesn’t keep going and produce corrupt data.
The Gear Check (need): Before a single byte is encrypted, the script checks if all tools (tar, gpg) are present. If something is missing, it won’t even start.
Create the file:
nano ~/Scripts/encrypt-folder.sh
Paste the following code:
#!/usr/bin/env bash
# encrypt-folder.sh — Pack and encrypt folder losslessly (AES-256),
# without plaintext intermediate files. Generates a .sha256 checksum.
# Phone (GrapheneOS/Termux): Output to ~/storage/downloads
# PC (Linux Desktop): Output to $HOME
set -Eeuo pipefail
umask 077
# -------------------- Helpers --------------------
die() { printf "❌ %s\n" "$*" >&2; exit 1; }
need() { command -v "$1" >/dev/null 2>&1 || die "Required program missing: $1"; }
need tar
need gpg
need sha256sum
# Determine target output based on system
OUT_DIR="$HOME"
if [ -d "$HOME/storage/downloads" ]; then
OUT_DIR="$HOME/storage/downloads"
fi
# Input: optional as argument, otherwise prompt
INPUT="${1-}"
if [ -z "$INPUT" ]; then
printf "📁 Please enter the folder name: "
IFS= read -r INPUT
fi
[ -n "$INPUT" ] || die "No name entered."
# Normalize path
case "$INPUT" in
~/*) SRC="$HOME/${INPUT#~/}" ;;
storage/*) SRC="$HOME/$INPUT" ;;
/sdcard/Download/*)
SRC="$HOME/storage/downloads/${INPUT#/sdcard/Download/}" ;;
/storage/emulated/0/Download/*)
SRC="$HOME/storage/downloads/${INPUT#/storage/emulated/0/Download/}" ;;
/*) SRC="$INPUT" ;;
*)
if [ -d "$HOME/storage/downloads/$INPUT" ]; then
SRC="$HOME/storage/downloads/$INPUT"
else
SRC="$HOME/$INPUT"
fi
;;
esac
[ -e "$SRC" ] || die "Path not found: $SRC"
[ -d "$SRC" ] || die "This is not a directory: $SRC"
BASE="$(basename "$SRC")"
BASE_SAFE="${BASE// /_}"
OUT_FILE="$OUT_DIR/Encrypted_${BASE_SAFE}.tar.gz.gpg"
if [ -e "$OUT_FILE" ]; then
OUT_FILE="$OUT_DIR/Encrypted_${BASE_SAFE}_$(date +%Y-%m-%d_%H-%M-%S).tar.gz.gpg"
fi
printf "📦 Packing & Encrypting → %s\n" "$OUT_FILE"
tar -C "$(dirname "$SRC")" -cz "$BASE" \
| gpg --symmetric --cipher-algo AES256 -o "$OUT_FILE" \
|| die "gpg failed"
sha256sum "$OUT_FILE" > "${OUT_FILE}.sha256"
printf "✅ Done:\n %s\n %s\n Location: %s\n" \
"$(basename "$OUT_FILE")" "$(basename "${OUT_FILE}.sha256")" "$OUT_DIR"
(Save in nano with CTRL+O, Enter, then CTRL+X)
────────────────
Part 2: The Mobile Key (Decryption)
On the go, cloud services often rename files. File.gpg suddenly becomes File.gpg.pgp or File (1).gpg. This script is the “Cloud Edition” — it finds your file even with incorrect extensions and verifies the SHA256 sum.
Create the file:
nano ~/Scripts/decrypt-folder.sh
Paste the following code:
#!/usr/bin/env bash
# decrypt-folder.sh (Cloud Edition)
# - Finds .gpg AND .pgp (double extension caused by Cloud/Download)
# - Smart SHA-Check (checks even if .pgp extension is added)
set -Eeuo pipefail
umask 077
export GPG_TTY="${GPG_TTY:-$(tty 2>/dev/null || true)}"
DL_DIR="$HOME/storage/downloads"
die(){ printf "❌ %s\n" "$*" >&2; exit 1; }
# --- 1. Automatic File Selection (GPG & PGP) ---
NAME="${1-}"
INPUT=""
if [ -z "$NAME" ]; then
LATEST="$(ls -t "$DL_DIR"/*.gpg "$DL_DIR"/*.pgp 2>/dev/null | head -n1 || true)"
if [ -n "$LATEST" ]; then
INPUT="$LATEST"
printf "🤖 File found: %s\n" "$(basename "$INPUT")"
else
printf "No file found. Enter name: "
IFS= read -r NAME
[ -n "$NAME" ] || die "Aborted."
fi
fi
if [ -z "$INPUT" ]; then
VARIANTS=(
"${NAME}"
"${NAME}.gpg"
"${NAME}.pgp"
"${NAME}.gpg.pgp"
"Encrypted_${NAME}.gpg"
)
for v in "${VARIANTS[@]}"; do
if [ -f "$PWD/$v" ]; then INPUT="$PWD/$v"; break; fi
if [ -f "$DL_DIR/$v" ]; then INPUT="$DL_DIR/$v"; break; fi
done
fi
[ -n "$INPUT" ] || die "Source file not found."
# --- 2. Intelligent SHA256 Check ---
SHA_CANDIDATE_1="${INPUT}.sha256"
SHA_CANDIDATE_2="${INPUT%.pgp}.sha256"
SHA_FILE=""
if [ -f "$SHA_CANDIDATE_1" ]; then
SHA_FILE="$SHA_CANDIDATE_1"
elif [ -f "$SHA_CANDIDATE_2" ]; then
SHA_FILE="$SHA_CANDIDATE_2"
echo "ℹ️ Correcting SHA path (ignoring .pgp extension)..."
fi
if [ -n "$SHA_FILE" ]; then
printf "🔎 Checking Integrity (SHA256)..."
EXPECTED=$(awk '{print $1}' "$SHA_FILE")
ACTUAL=$(sha256sum "$INPUT" | awk '{print $1}')
if [ "$EXPECTED" = "$ACTUAL" ]; then
echo " ✅ OK."
else
echo " ❌ ERROR!"
echo " WARNING: Checksums do not match!"
echo " File might be corrupt."
printf " Proceed anyway? (y/N) "
read -r -n 1 REPLY
echo
if [[ ! $REPLY =~ ^[Yy]$ ]]; then
die "Aborted."
fi
fi
else
echo "ℹ️ No .sha256 file found (Check skipped)."
fi
# --- 3. Decrypt & Extract ---
printf "🔓 Decrypting & Extracting..."
if gpg --quiet --decrypt "$INPUT" | tar -xz; then
echo " ✅ Done."
echo "📂 Folder located in: $PWD"
elif gpg --quiet --pinentry-mode loopback --decrypt "$INPUT" | tar -xz; then
echo " ✅ Done."
echo "📂 Folder located in: $PWD"
else
die "Error."
fi
Make both scripts executable:
chmod +x ~/Scripts/encrypt-folder.sh ~/Scripts/decrypt-folder.sh
────────────────
The Workflow in the Field
Scenario A: Encrypt and Decrypt on Phone
You have a folder (e.g., Finance) in your Download area.
- Open Termux.
- Run:
~/Scripts/encrypt-folder.sh - Type the folder name:
Finance - Result:
Encrypted_Finance.tar.gz.gpgand the checksum are now in your Download folder.
To decrypt: run ~/Scripts/decrypt-folder.sh. The decrypted files will be in the Termux Home directory.
Scenario B: Decrypting Data from PC (The Emergency Case)
You transferred an encrypted file (e.g., Encrypted_Backup.tar.gz.gpg) from your PC to your phone.
- Ensure the file is in the Android Download folder.
- Open Termux and run:
~/Scripts/decrypt-folder.sh - The script decrypts the data into the Termux Home directory. Open your “Files” app — find the
Termuxentry in the sidebar. Your decrypted folder lies there.
────────────────
Why Auditability Is King
You could download an app called “AES Safe Box.” But do you know what it does with your keys?
With these scripts, you see every command:
Tar packs. GPG encrypts. SHA256 verifies.
No magic. Just math.
────────────────
The Full Series
👉 Part 1 — Desktop Scripts: https://primal.net/Alien-Investor/the-digital-bunker-scripting-sovereignty 👉 Part 3 — Command Line Comfort (Aliases): https://primal.net/Alien-Investor/the-digital-bunker-command-line-comfort
────────────────
🧰 Tools for True Owners (Affiliates — Support at No Extra Cost)
Tools I use myself — for Bitcoin self-custody and digital sovereignty:
📕 Alien Investor Guides: My own eBook “GrapheneOS: Android in the Surveillance Age” — the complete step-by-step guide to hardening your phone against the surveillance state. 👉 https://alien-investor.org/buecher
💥 21bitcoin: Bitcoin-only app from Europe, ideal for DCA and stacking sats regularly — no shitcoins. Use code ALIENINVESTOR for a permanent 0.2 percentage point fee reduction on instant and savings plan purchases. 👉 https://alien-investor.org/21bitcoin
₿ BitBox: Hardware wallet for secure self-custody. I use the BitBox — available as the classic BitBox02 and the new BitBox for iPhone (Nova). Use code ALIENINVESTOR for 5% off. 👉 https://alien-investor.org/bitbox
🛡️ Proton: Swiss all-round protection for email, VPN, and cloud — privacy-first, no Big Tech dependency. 👉 https://alien-investor.org/proton
Disclaimer: Some of these links are affiliate links. If you use them, you support my work at no extra cost to you. Thank you!
────────────────
Money, power, Bitcoin — and OPSEC. I write about financial sovereignty, privacy, and cybersecurity in a world built on control. More at alien-investor.org (German only) 👽